Question & Answer
Question
What do I need to know and what are the frequently asked questions about the QRadar X-Force Threat Intelligence feed?
Cause
Quick links
- How to Enable X-Force Threat Intelligence
- Downloading X-Force rule content for QRadar
- What is the X-Force Threat Intelligence feed for QRadar?
- Firewalls and X-Force data updates
- How to configure X-Force feeds with proxy servers
- Rules are grouped by "Enhanced X-Force Rules" and "Legacy Rules". How are these rule groups different?
- Advanced Searches (AQL) with IBM X-Force
- What is confidence factor?
- Reporting an incorrect IP address, URL, or categorization in X-Force to IBM
- How to report IP addresses or URLs in bulk for incorrectly categorized sites
Answer
How to enable X-Force Threat Intelligence
X-Force Threat Intelligence feeds no longer needs to be purchased as a separate subscription. It is included with the standard license as part of Service & Support. Administrators who previous did not have IP and URL reputation data licensed and want to enable X-Force Threat Intelligence feeds can now enable this feature from the System Settings screen of the Admin tab. Any users who do not upgrade to QRadar 7.2.8 remain on their existing subscription model until they upgrade to a supported version (QRadar 7.4.x or later).
To enable X-Force Threat Intelligence feeds for QRadar
This procedure is not required for most users and is typically enabled by default. If you experience issues with X-Force rules, you can confirm the System Setting in QRadar.
- Log in to QRadar as an administrator.
- Click the Admin tab.
- Click the System Settings icon.
- From the Enable X-Force Threat Intelligence Feed drop-down, select Yes.

- Click Save.
- From the Admin tab, click Deploy Changes to enable the X-Force Threat Intelligence Feed for the deployment.
NOTE: Administrators must allow Internet access from the QRadar Console to the following addresses to get X-Force Threat Intelligence Feed data from IBM. The following servers are contacted for both X-Force data updates, licensing, dashboard widget feeds, and QRadar automatic updates:Server contacted Server description update.xforce-security.com X-Force Threat Intelligence Feed update server for IP reputation and URL data license.xforce-security.com X-Force Threat Intelligence licensing server
What to do next
After the X-Force Threat Intelligence Feed is enabled, administrators who are on new installs need to verify that they have Threat Monitoring Content Extension installed. This procedure is discussed in the next section and enables X-Force rules to be enabled that work with the Threat Intelligence Feed.
Downloading X-Force rule content for QRadar
Administrators can install rule content that is pertinent to them instead of using the full default ruleset. If you are a new administrator, you can review for available content extensions to expand the base rules for QRadar, including X-Force Premium Rules. These content extensions add rules, building blocks, reports, and other types of data to build the baseline QRadar rule set. After a new install of QRadar is completed, administrators are encouraged to review and install these extensions from the IBM X-Force Exchange.
IMPORTANT: To add X-Force Rules to QRadar, administrators must install the QRadar Threat Monitoring Content Extension.
List of Common QRadar Rule Content Extensions:
| Extension Name | Required for X-Force Premium Users? |
Description
|
| IBM QRadar Security Threat Monitoring Content |
Yes
|
Threat Monitoring Content rules focus on threat indicators and integration with threat intelligence feeds, such as IBM X-Force premium rules. X-Force Premium rules can be leveraged on event or flow data as they are common rules in QRadar. The following IP-based rules can generate offenses when: 1. The Threat Monitoring Content Extension is installed. 2. The rule is enabled. 3. The X-Force Feed is enabled in QRadar (System Settings) and Firewalls, or Proxies, are configured. IP Rules IP rules leverage basic categories and confidence factor during evaluating of events or flows. Categories can be anonymization server, botnet C&C, botnet, malware, dynamic IP addresses, Scanning IP addresses, or spam. The following IP-based rules are added to QRadar when an IP of the category meets the confidence factor assigned to that IP address. By default, these rules use a confidence factor of 75 or greater.
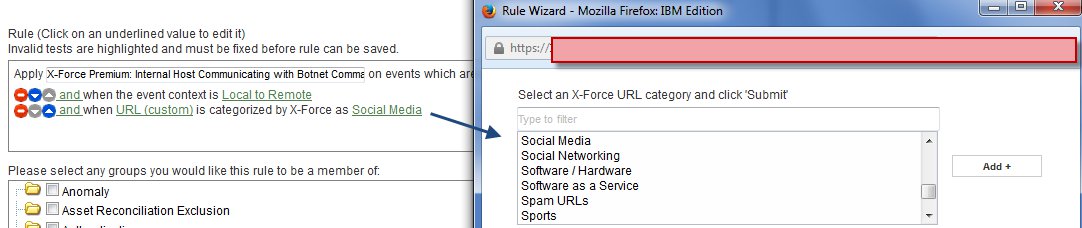
URL rules leverage categories for websites, instead of confidence factor. Categories can be botnet, spam, gambling, job search, adult, and so on. When X-Force premium is licensed, the following URL-based rules are added to QRadar. URL based rules can be leveraged by events that contain URLs as a custom property URL(custom), and trigger against categorization of the URL itself.
|
| IBM Security Anomaly Content |
No
|
The Anomaly extension adds 10 anomaly rules and 9 building blocks for a total of 19 content add-ons for QRadar. |
| IBM Security Compliance Content |
No
|
The Compliance extensions add: 4 custom event properties, 42 event searches, 7 flow searches, 153 reports, 140 rules and building blocks, and 10 reference data sets. |
| IBM Security Intrusion Content |
No
|
The Intrusion extension adds 20 intrusion rules, 52 building blocks, and one reference data set for a total of 73 content add-ons for QRadar. |
| IBM Security ISO 27001 Content |
No
|
The ISO 27001 extension adds: 4 custom event properties, 29 event searches, 77 reports, 4 rules, and 31 building blocks. For a total of 145 content add-ons for QRadar. |
| IBM Security Reconnaissance Content |
No
|
The Recon extension adds 10 reference sets, 62 rules, and 42 building blocks for a total of 114 content add-ons for QRadar. |
What is the X-Force Threat Intelligence feed for QRadar
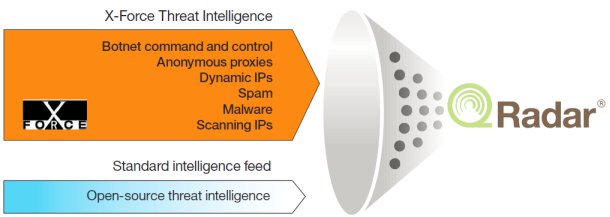
The IBM Security X-Force Threat Intelligence provides two levels of data to customers, both a free basic feed and subscription-based premium feed for QRadar users. On all QRadar supported versions, the premium X-Force Threat Intelligence feeds are a core feature as part of the appliance support license. X-Force uses a series of data centers across the globe to collect tens of thousands of malware samples, analyze web pages and URLs, and running IP address analysis to categorize IP address information. By categorizing IP addresses into segments such as malware hosts, spam sources, and anonymous proxies, this IP reputation data can be incorporated into QRadar rules, offenses, and events. IP categorization allows for capturing events more quickly and accurately than previously possible, as well as for capturing them in a way that provides more understanding for further analysis.
Firewalls and X-Force data updates
QRadar is updated daily with a new X-Force IP reputation and URL data. This data is provided when new IP reputation or URL database information is available. These checks occur every minute and it is possible for QRadar to be updated multiple times per day with new data, with new IP information provided every 2 minutes and URL data every 5 minutes. The updates are merged into their own databases and the content is replicated from the Console out to the managed hosts in the deployment. In older versions of QRadar (7.2.3 or earlier), the X-Force data was provided by using QRadar automatic updates.
The following servers are contacted for both X-Force data updates, licensing, dashboard widget feeds, and QRadar automatic updates:
| Server contacted | Server description |
| update.xforce-security.com | X-Force Threat Intelligence Feed update server for IP reputation and URL data |
| license.xforce-security.com | X-Force Threat Intelligence licensing server |
| auto-update.qradar.ibmcloud.com/ | QRadar automatic updates are now at htts://auto-update.qradar.ibmcloud.com/. For more information, see: https://www.ibm.com/support/pages/node/6244622. |
The X-Force data provided includes IP reputation data, URL data, and categorization data. Administrators are to expect that these updates consume bandwidth daily. The following list contains the approximate daily bandwidth usage for all data types:
- IP Reputation (IPR) Data: 16 MB
- WEB/URL Data: 5 MB
- Web Application Categorization Data: 100 KB
How to configure X-Force feeds with proxy servers
The answer to X-Force feeds configuration depends on the version of QRadar that is installed on your Console.
In all supported QRadar versions (7.2.x and later), a change was made so that X-Force IP reputation data was unlinked from the automatic update process. QRadar updates no longer use the proxy settings from the automatic updates screen on the Admin tab for X-Force data updates. X-Force servers provide data to each managed host's database and the IP reputation and URL lookup database is kept locally for evaluating rules. QRadar uses a reverse proxy lookup through Apache on the QRadar Console to collect data directly from X-Force servers on the Internet. All QRadar appliances in the deployment (includes the Console), contacts Apache on the Console in order to get a cached request out to the X-Force servers. After the data is received by the Console, lookups and other data still required are passed through the Console, for unauthenticated proxies. If you have authenticated proxies in your network, the managed host must make a direct request.
CRITICAL
If your proxy requires any type of authentication, you must configure basic authentication on the Console and each managed host. Authenticated proxies cannot forward the authentication details to your proxy server from the Console and requests are dropped by the authenticated proxy. To resolve this issue, you must allow each managed host to directly talk to the proxy so they can then authenticate and get updates from X-Force servers. If you have unauthenticated proxies, all traffic can transition through the Console.
Option 1: Unauthenticated proxy server configuration
If you are using a proxy in your network, administrators need to update HTTPd on the Console in order to pass-through the existing request. In addition, to send the request through the proxy server in order to receive the X-Force data. Note: NTLM authentication is not supported. Back up all files you edit to another location such as the store/IBM_Support before you manually edit any files.
In all supported QRadar versions (7.2.x and later), a change was made so that X-Force IP reputation data was unlinked from the automatic update process. QRadar updates no longer use the proxy settings from the automatic updates screen on the Admin tab for X-Force data updates. X-Force servers provide data to each managed host's database and the IP reputation and URL lookup database is kept locally for evaluating rules. QRadar uses a reverse proxy lookup through Apache on the QRadar Console to collect data directly from X-Force servers on the Internet. All QRadar appliances in the deployment (includes the Console), contacts Apache on the Console in order to get a cached request out to the X-Force servers. After the data is received by the Console, lookups and other data still required are passed through the Console, for unauthenticated proxies. If you have authenticated proxies in your network, the managed host must make a direct request.
CRITICAL
If your proxy requires any type of authentication, you must configure basic authentication on the Console and each managed host. Authenticated proxies cannot forward the authentication details to your proxy server from the Console and requests are dropped by the authenticated proxy. To resolve this issue, you must allow each managed host to directly talk to the proxy so they can then authenticate and get updates from X-Force servers. If you have unauthenticated proxies, all traffic can transition through the Console.
Option 1: Unauthenticated proxy server configuration
If you are using a proxy in your network, administrators need to update HTTPd on the Console in order to pass-through the existing request. In addition, to send the request through the proxy server in order to receive the X-Force data. Note: NTLM authentication is not supported. Back up all files you edit to another location such as the store/IBM_Support before you manually edit any files.
- Log in to the QRadar Console as the root user.
- Edit the /etc/httpd/conf.d/ssl.conf file.
- Add the following lines before </VirtualHost> in the ssl.conf file:
Note: Administrators must update step 3 with the IP address and port of the corporate proxy server. This step requires that the proxy allows an anonymous (no credentials) connection to the x-force-security servers.ProxyRemote https://license.xforce-security.com/ http://PROXY_IP:PROXY_PORT ProxyRemote https://update.xforce-security.com/ http://PROXY_IP:PROXY_PORT - Save the changes to the ssl.conf file.
- Edit the /store/dca/server.ini file.
- Add the following information to the server.ini file:
# # Configure proxy settings # [proxy_server] <type your proxy server IP address here or URL> [proxy_port] <type your proxy port here> - Save the changes to the server.ini file.
- Type the following command to restart the Apache server on the Console and scaserver:
apachectl restart && systemctl restart scaserverImportant: Restarting the Apache server on the QRadar Console logs out all users and the managed hosts might produce error messages. Restart the Apache server during scheduled maintenance windows.
Option 2: Basic Authentication for Proxy Servers
For administrators who use basic authentication on their proxy server, they can configure their proxy settings in the server.ini file on the QRadar Console. Before you begin, it is advised to back up all files you edit to another location, such as /store/IBM_Support.
CRITICAL
If your proxy requires any type of authentication, this procedure must be repeated on each managed host. Authenticated proxies cannot forward the authentication details up to the proxy server from the Console and requests are dropped by the authenticated proxy. To resolve this issue, you must allow each managed host to directly talk to the proxy so they can then authenticate and get updates from X-Force servers.
If your proxy requires any type of authentication, this procedure must be repeated on each managed host. Authenticated proxies cannot forward the authentication details up to the proxy server from the Console and requests are dropped by the authenticated proxy. To resolve this issue, you must allow each managed host to directly talk to the proxy so they can then authenticate and get updates from X-Force servers.
Procedure
- Log in to the QRadar Console as the root user.
- Edit the /store/dca/server.ini file.
- Add the following information to the server.ini file:
# # Configure proxy settings # [proxy_server] (type your proxy server IP address here) [proxy_port] (type your proxy port here) [proxy_user] (type your proxy username here) [proxy_pass] (type your proxy password here) - Save the changes to the server.ini file.
- Edit the /opt/qradar/systemd/bin/scaserver_update_settings.sh file.
- Add exit 0 to the second line. For example,
#!/bin/sh exit 0 SCRIPT_NAME=$(basename "$0") -
Save the changes to the scaserver_update_settings.sh file.
- Edit the /store/dca/dca/init/dca_license/dca_license_settings_user.txt file.
- In the [license_server] field, update the URL to: https://license.xforce-security.com/license_v4.asp
For example,[license_server] https://license.xforce-security.com/license_v4.asp - Save the changes to the license settings file.
- Edit the /store/dca/dca/init/dca_update/dca_update_settings_user.txt file.
- Update the download and upload server URLs to the following values:
[update_download_server] https://update.xforce-security.com/version6/dca_update6.asp [update_upload_server] https://update.xforce-security.com/version6/of_upload.asp - Save the changes to the license settings file.
- To restart the scaserver and load the file changes, type:
Important: Restarting the Apache server on the QRadar Console logs out all users and the managed hosts might produce error messages. Restart the Apache server during scheduled maintenance windows.apachectl restart && systemctl restart scaserver - Repeat this procedure on any managed hosts, such as Event Processors or Flow Processors that require X-Force data to evaluate rules.
NOTE
Administrators who continue to experience issues after the scaserver restart might be experiencing APAR IJ18011. This issue overwrites the changes made to dca_license_settings_user.txt and dca_license_settings_user.txt. If your changes are not preserved or you do not receive X-Force data after updating your proxy settings, ensure you are updated to QRadar 7.4.3 or later. If you continue to have issues, then contact QRadar Support for assistance with IJ18011 referenced.
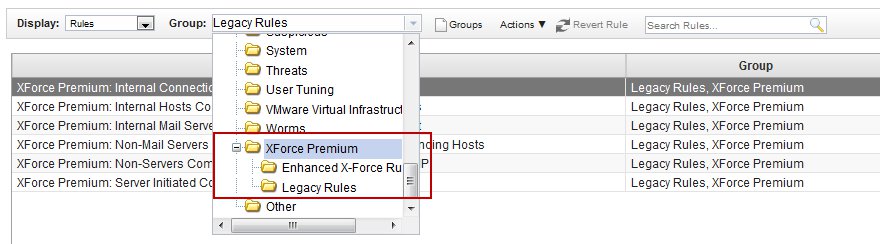
Rules are grouped by "Enhanced X-Force Rules" and "Legacy Rules". How are these rule groups different?
The original version of X-Force common rules in QRadar evaluated the source or destination IP addresses in events or flows against the list of X-Force addresses. In QRadar newer versions, the X-Force rules were enhanced to not only support IP-based rule tests, but to also support URLs for event rules, and a new value called, 'confidence factor'. To ensure that user rules were not corrupted after an update, we split the rules as two separate groups. These groups are listed under the X-Force Premium rules group as "Enhanced X-Force Rules" and "Legacy rules".
NOTE: Legacy X-Force rules are only shown if you upgraded from a previous version of QRadar.
An example of an X-Force legacy rule:
"when the [source IP|destinationIP|any IP] is part of any of the following [remote network locations]"
An example of an IP address and URL X-Force enhanced rule:
"when [this host property] is categorized by X-Force as [Anonymization Servers|Botnet C&C|DynamicIPs|Malware|ScanningIPs|Spam] with confidence value [equal to] [this amount]" (Based on IP address)
"when [this URL property] is categorized by X-Force as [Gambling|Auctions|Job Search|Alcohol|Social Networking|Dating|etc]" (Based on URL)
Advanced Searches (AQL) with IBM X-Force?
Yes, users can leverage advanced searches to return data from X-Force Exchange from the Log Activity or Network Activity tab in QRadar.
| Description | Example advanced search |
| To search for source IP addresses on an X-Force category with a confidence factor greater than 50. | select * from events where XFORCE_IP_CONFIDENCE('Spam',sourceip)>50 |
| To search for X-Force categories associated to a URL. | select url, XFORCE_URL_CATEGORY(url) as myCategories from events where XFORCE_URL_CATEGORY(url) IS NOT NULL |
| To search for X-Force categories associated to an IP a source IP address. | select sourceip, XFORCE_IP_CATEGORY(sourceip) as IPcategories from events where XFORCE_IP_CATEGORY(sourceip) IS NOT NULL |
- Log in to the QRadar user interface.
- Click the Log Activity tab.
- Select Advanced Search from the drop-down on the Search toolbar.
- Type an advanced search expression.
For example,

- Click Search.
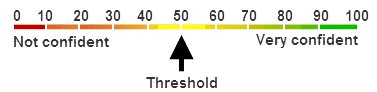
What is confidence factor?
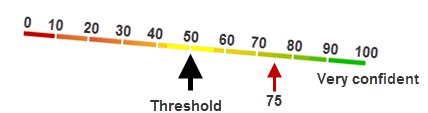
Confidence factor is values assigned to IP Reputation data that represents how confident X-Force is that the data seen from the IP is categorized properly. Confidence factor is a probability scale that ranges 0 - 100 where a value of 50+ is the threshold where customers need to consider taking action on a triggered rule. IP reputation is evaluated on the time (first seen, last seen) and the volume of messages or data. For example, SPAM messages. An IP Reputation (Spam) entry of zero (0) indicates that the source IP traffic is definitely not spam whereas an entry of 100 indicates definite spam traffic. Consider a value of 50 to be a threshold. Thus, values less than 50 indicate less likelihood that spam is present, and values greater than 50 indicate more likelihood that spam is present. These probabilities are based on massive amounts of ongoing web-based data that IBM X-Force continuously collects and analyzes from around the world in X-Force data centers. As data is collected, the system evaluates "How much spam did we see from an IP address", or "How frequently is this SPAM flagged IP address showing up in the IP Reputation category". The more times that we see values, the higher the system scores the confidence factor.
Categorization and the Confidence Factor can be viewed when you investigate an IP address or URL in the X-Force Exchange.

When rules are tuned, think of a scale where 50 is the tipping point. On assets of lower importance, an administrator might weigh an X-Force rule to trigger a higher confidence factor (75) for specific categories like SPAM. Increasing the trigger value reduces the number of offenses generated on a lower priority system and noncritical assets. Tuning the rule higher means that the IP that the rule triggers only when X-Force sees an IP address at or above a confidence factor of 75. An important system or critical business asset might be tuned to trigger the rule at a confidence factor of 50. Lowering the confidence value triggers an offense at a lower level, and can bring attention to an issue more quickly for a business-critical system.
Is there a location where I can look up and investigate IP address information?
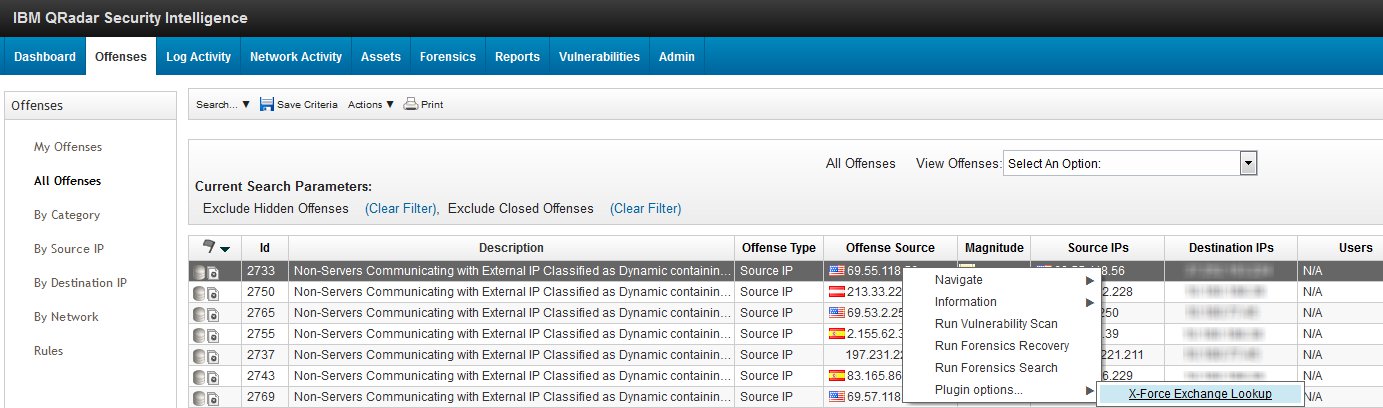
Yes, we recommend that customers leverage IBM X-Force Exchange to gather information and lookup IP addresses related to botnets, spam, and malware categories. There is a right-click plug-in in QRadar by default where administrators can review and investigate IP addresses and URLs directly from QRadar with a right-click menu. This plug-in is installed by default in QRadar 7.2.5 systems. In most cases, QRadar rules use a default threshold of 75 is an acceptable value for a rule, because it defines a high level of probability that the data is correct per the classification based on what is known. For information on the X-Force Exchange right-click plug-in, see QRadar: IBM X-Force Exchange right-click plug-in FAQ.
Reporting an incorrect IP address, URL, or categorization in X-Force to IBM
If administrators believe that an IP address or URL is being misclassified by X-Force, they should report this issue by commenting on the IP, or URL, on the X-Force Exchange website. All comments and updates are monitored by IBM, so any comments created by an authenticated user is reviewed by the X-Force team. Comments are not permitted for 'Guest' accounts on the X-Force Exchange website.How to report an issue to the X-Force Exchange team from QRadar
- Log in to QRadar.
- Right-click on an IP address or URL and select X-Force Exchange Lookup. (Optionally, navigate to https://exchange.xforce.ibmcloud.com/)
The X-Force Exchange website is launched and displays the information and confidence percentage of the IP address or URL categorization. - Select the I agree to the Terms of Service check box.
- Click Log in.
Note: you must log in before you can comment. Guests are not allowed to submit comments on IP addresses or URLs. - Click the Suggest Edit button.
- Complete the submission form to comment on the IP address or URL.

- To receive updates on your comment, make sure you select Yes on the 'Stay Informed' option.
- Click Submit.
- After the comment is submitted, it will be reviewed by the X-Force Exchange team. If you selected to stay informed, feedback is provided by the X-Force Exchange team.
How to report IP addresses or URLs in bulk for incorrectly categorized sites
If administrators have a large number of IP addresses, or URLs, that are misclassified by X-Force, or believed to be incorrect, they should report this issue to QRadar Support instead of trying to input comments by hand. QRadar administrators can provide a list of IP addresses or URLs to a QRadar Support Representative and they pass this information to the X-Force team for resolution. The URLs or IP addresses are reviewed by the X-Force team for resolution allowing administrators to submit data without having to enter comments by hand for many sites or IP addresses.How to report categorization issues in bulk
- Open an IBM Service Request for QRadar.
- Provide the list of IP addresses or URLs for X-Force review in your service request.
- The support representative contacts you using your preferred method of communication to confirm and clarify any questions from your request.
- The URL and IP address information is forwarded to the X-Force team on your behalf.
[{"Line of Business":{"code":"LOB24","label":"Security Software"},"Business Unit":{"code":"BU059","label":"IBM Software w\/o TPS"},"Product":{"code":"SSBQAC","label":"IBM Security QRadar SIEM"},"ARM Category":[{"code":"a8m0z000000cwsyAAA","label":"Admin Tasks"}],"ARM Case Number":"","Platform":[{"code":"PF016","label":"Linux"}],"Version":"All Version(s)"}]
Was this topic helpful?
Document Information
Modified date:
04 August 2023
UID
swg21701213